Table of contents:
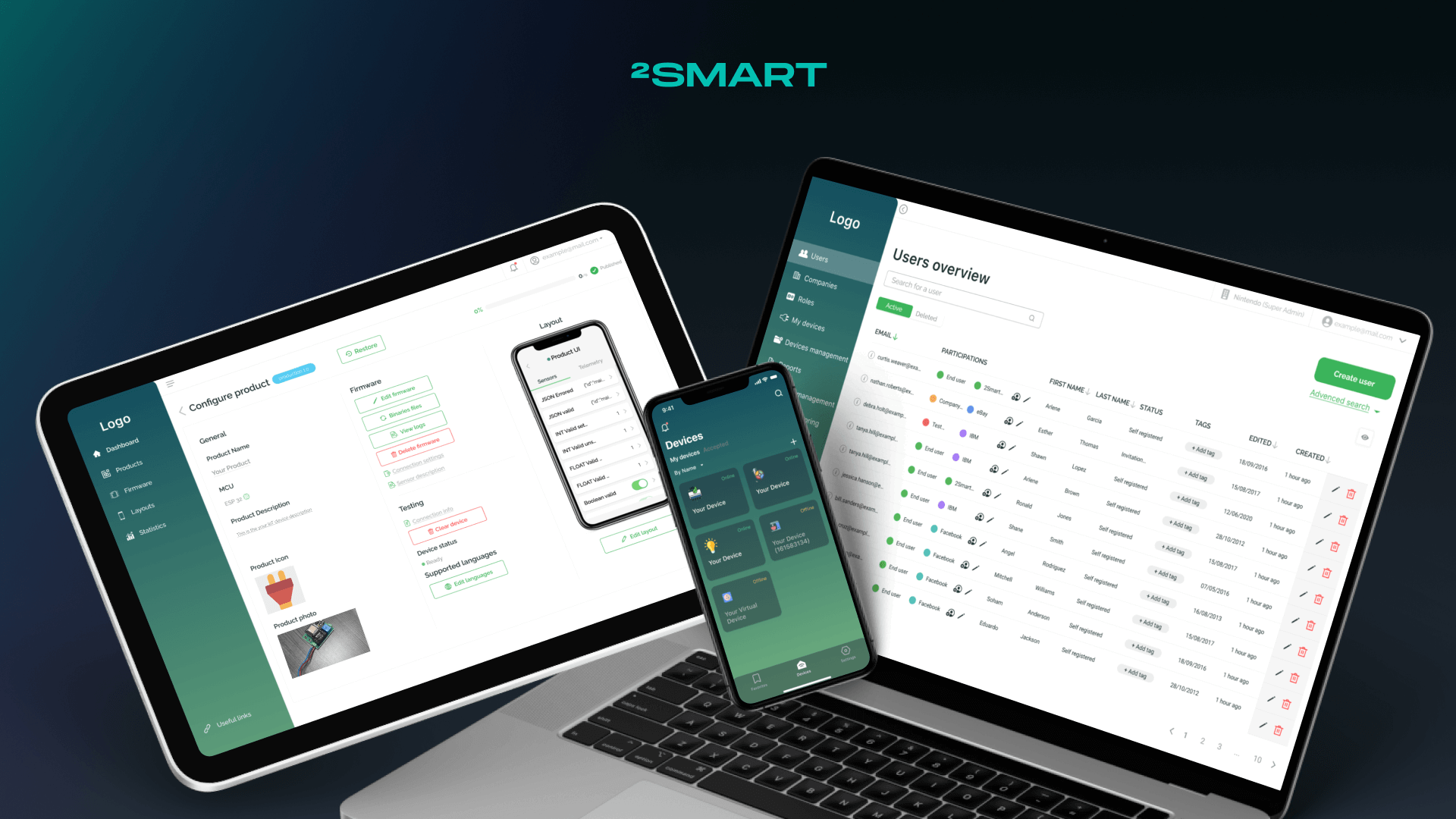
Permissions for users to perform certain actions within the IoT platform are determined by the roles configured for them. At the same time, within the framework of a multi-tenant IoT platform, the same user can be a member of several companies, which means that the options for setting roles should take this into account. The 2Smart team describes their vision of what perfect user and role management in an IoT platform looks like and how an enterprise can flexibly use this functionality for the business model it follows.
Users and Their Roles in the System: An Introduction
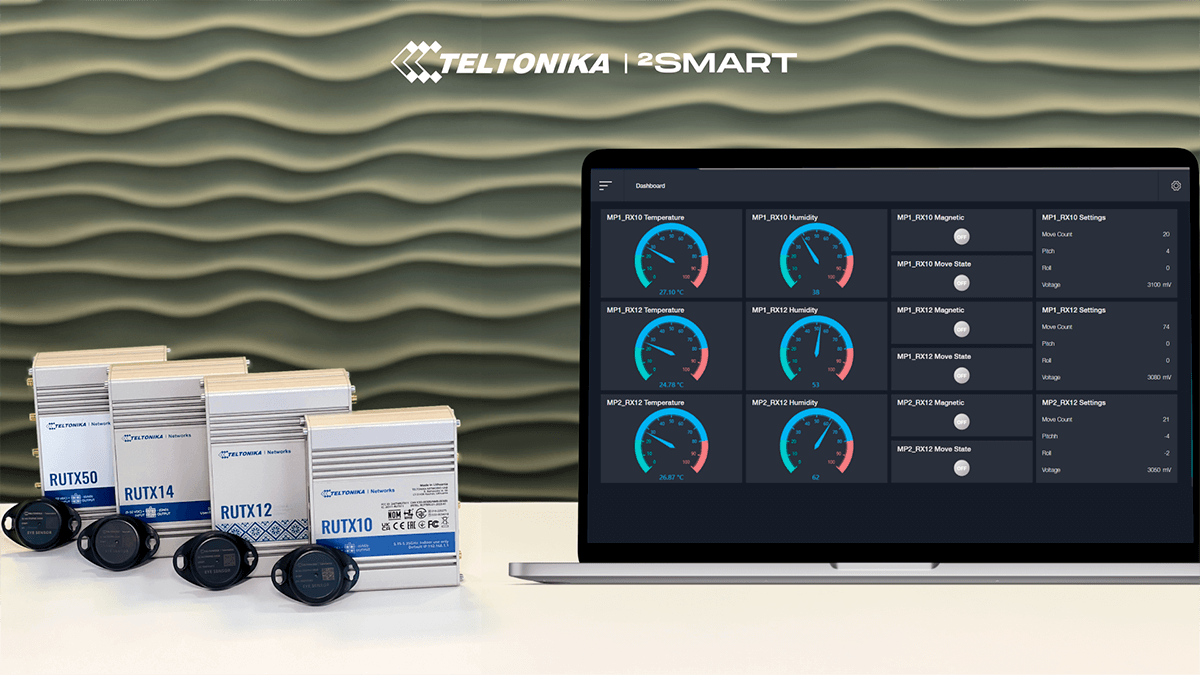
User and role management is a core feature of many enterprise IT solutions. Solution providers offer a different approach to the implementation of this functionality, and below we will talk about how the management of these entities is implemented in the 2Smart IoT Business Platform.
First of all, let’s reveal the essence of the terms discussed below:
- User – any member of the system. In the case of an IoT platform, this can be an end user of an IoT device connected to the platform, a developer, a technical specialist, a system administrator, etc.
- Role – the set of accesses and permissions available to the User.
- Company – an organization that is a system member and unites the users included in it.
Since the system user can be either a person who operates an IoT device connected to the platform, or a technical specialist or administrator, different participants need different permissions and privileges when working with the device and the system as a whole. This set of permissions is described as a user role.
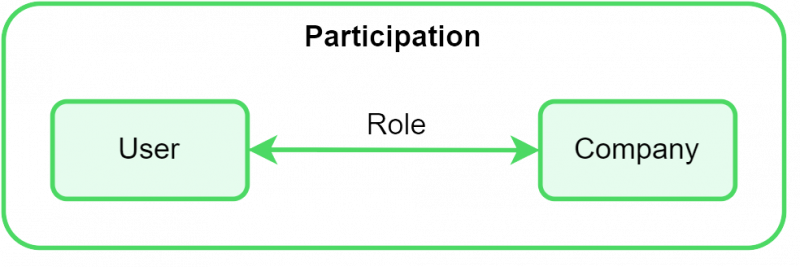
In addition, within an IoT platform with a multi-tenant architecture, it may be necessary for the same user to have different roles in different companies. A person can be a device end user in one company, a technician in another, and an administrator in a third. For a person to switch between their different roles in different companies within the same account, the 2Smart Business Platform uses an additional entity called Participations.
User Management in the 2Smart IoT Business Platform
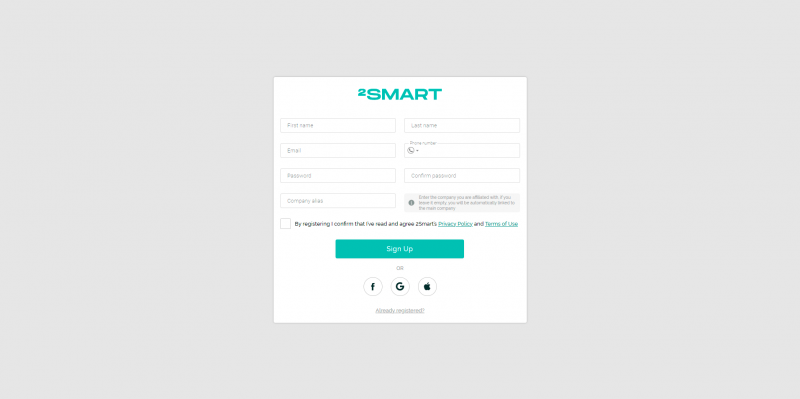
A person can obtain an IoT Business Platform user account in two ways:
- user registration by an administrator,
- self-registration in the platform.
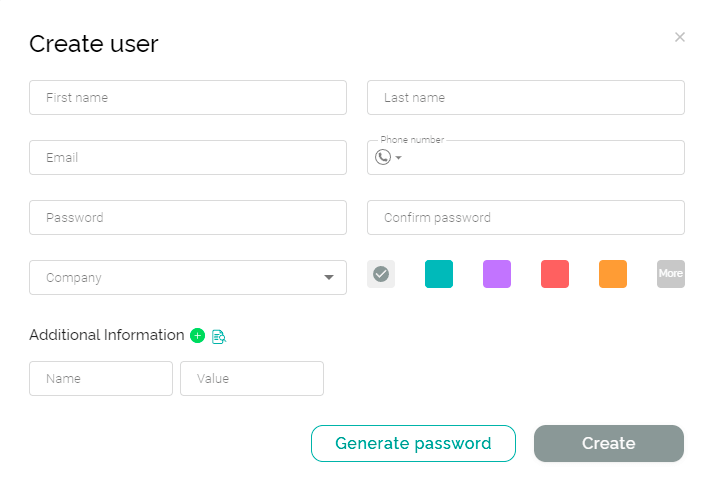
Administrators can add new users to the system knowing their emails. In this case, an account is created for each new user. The administrator can specify which company the user belongs to and what role they have in this company. The system will assign the user a password to log into the account, which they can later replace with their own.
After the administrator creates a new user, they receive an email invitation, and after confirming which, the person starts using the functionality of the IoT business platform.
In self-registration, a new user can specify the company they belong to but cannot specify a role. By default, they are assigned the “end user” role, and changing this role to another requires the action of a system administrator.
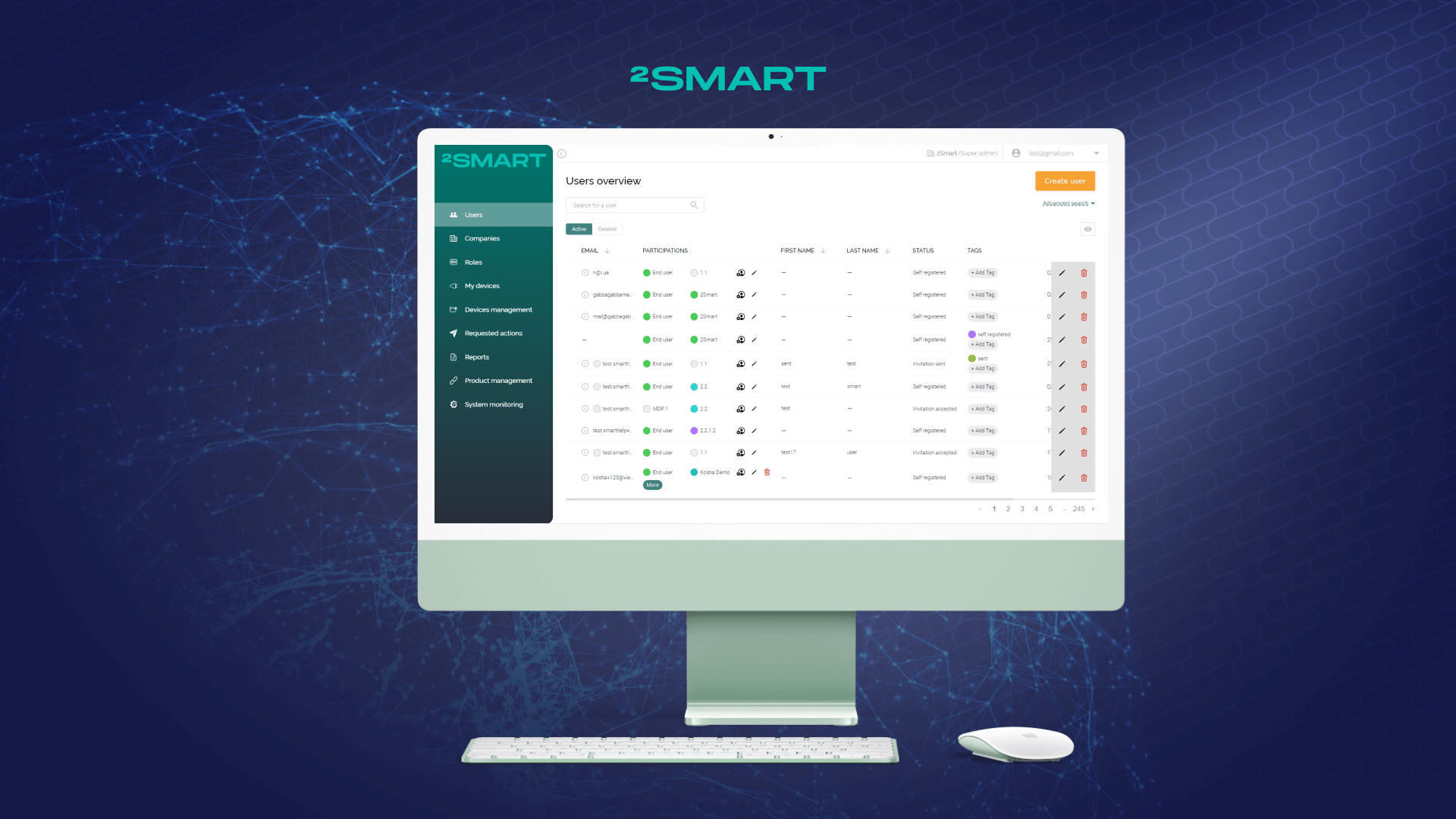
If we turn to user management by administrators, they can view the list of users in the system and create and edit their participations (roles in companies). Admins can also edit user data, such as clarifying their personal data, adding phone numbers and any other information to custom fields. Administrators can assign tags to users for flexible grouping, etc., and delete users from the system.
The list of permissions for admin’s role defines the specific actions that can be performed with users data. An administrator can have a role that allows only viewing the list of users without the ability to edit their data. The other extreme is unlimited permissions for any possible actions with users in the system.
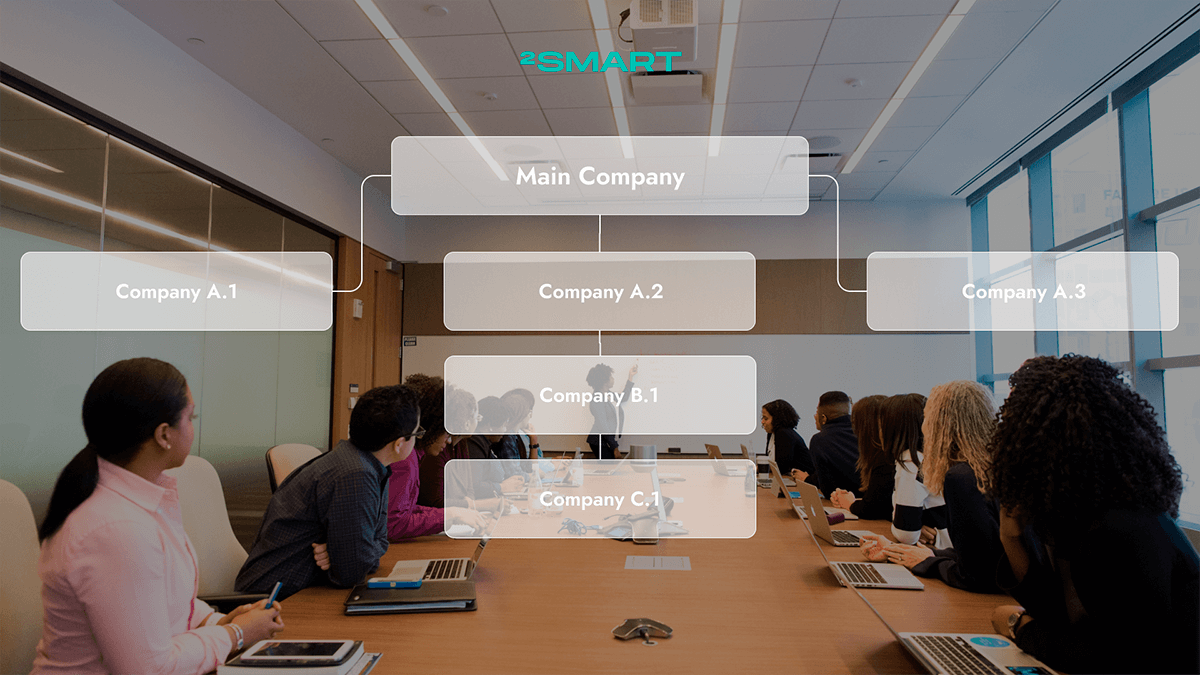
Within the framework of a multi-tenancy architecture of a Business Platform, the tree of companies can be quite branched. Therefore, when managing users, there is a limitation for administrators that allows them to see and manage only the users of their own company and its subsidiaries, as well as all lower-level companies that branch off from subsidiaries. Only administrators of the Main Company, which is at the highest level, can see and manage a complete list of all users of the system.
Role Management in the 2Smart IoT Business Platform
Default Roles
By default, there are three roles in the Business Platform for managing the IoT infrastructure of an enterprise, which cover approximately 80% of possible cases:
- Super Admin with a complete set of permissions, including unique ones.
- Company Admin with basic system management permissions.
- The end user of the device.
Within each company in the system, there can be one or more Super Admins. A user with this role can actually perform any action in the system without restrictions. A unique Super Admin permission that no other role has is the ability to create IDs to connect new devices to the system.
Company Admins have slightly fewer permissions than Super Admins but also have some unique ones. For example, they can view and manage requested actions, i.e., approve or decline some sensitive activities that users with other roles want to perform.
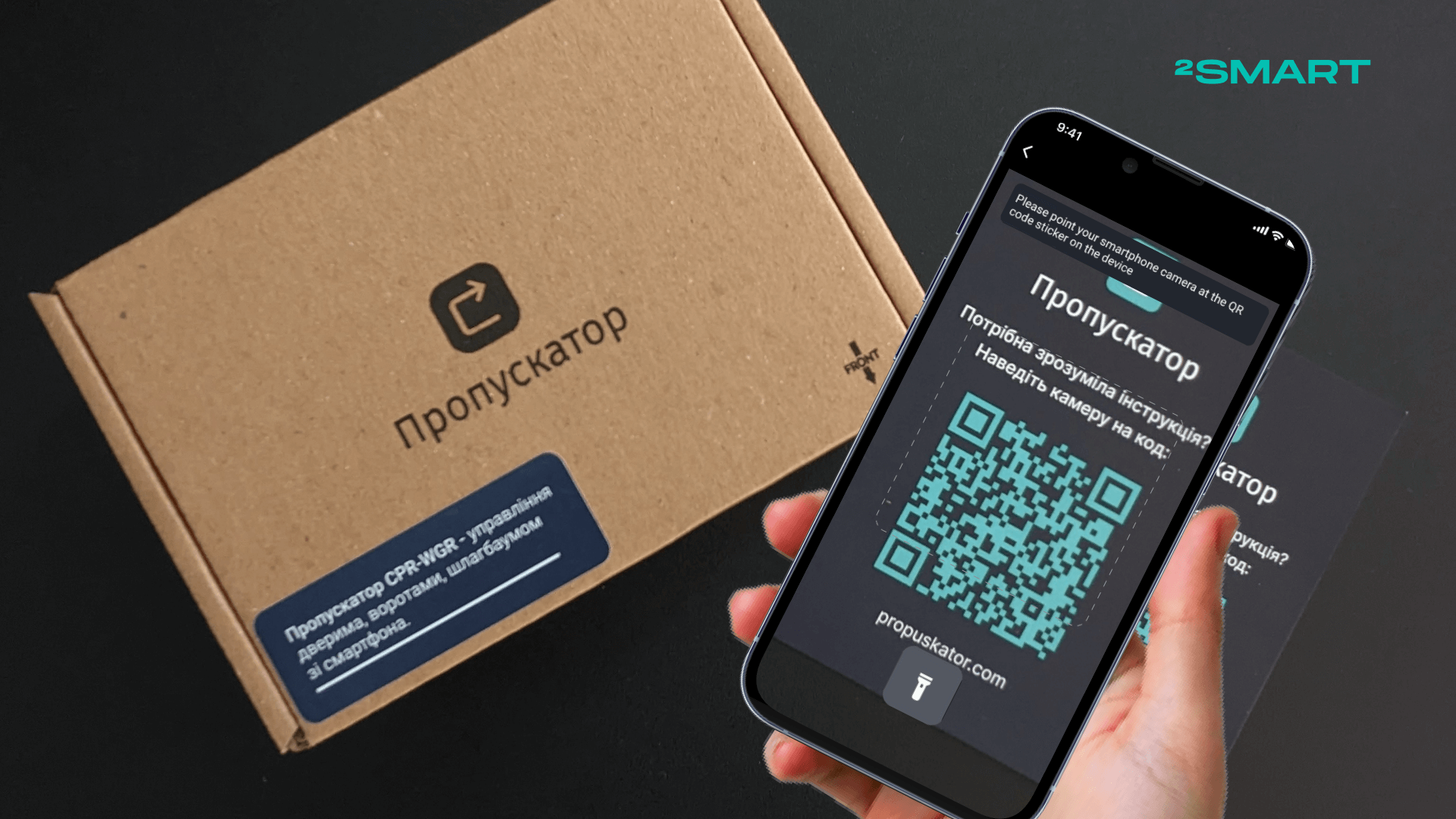
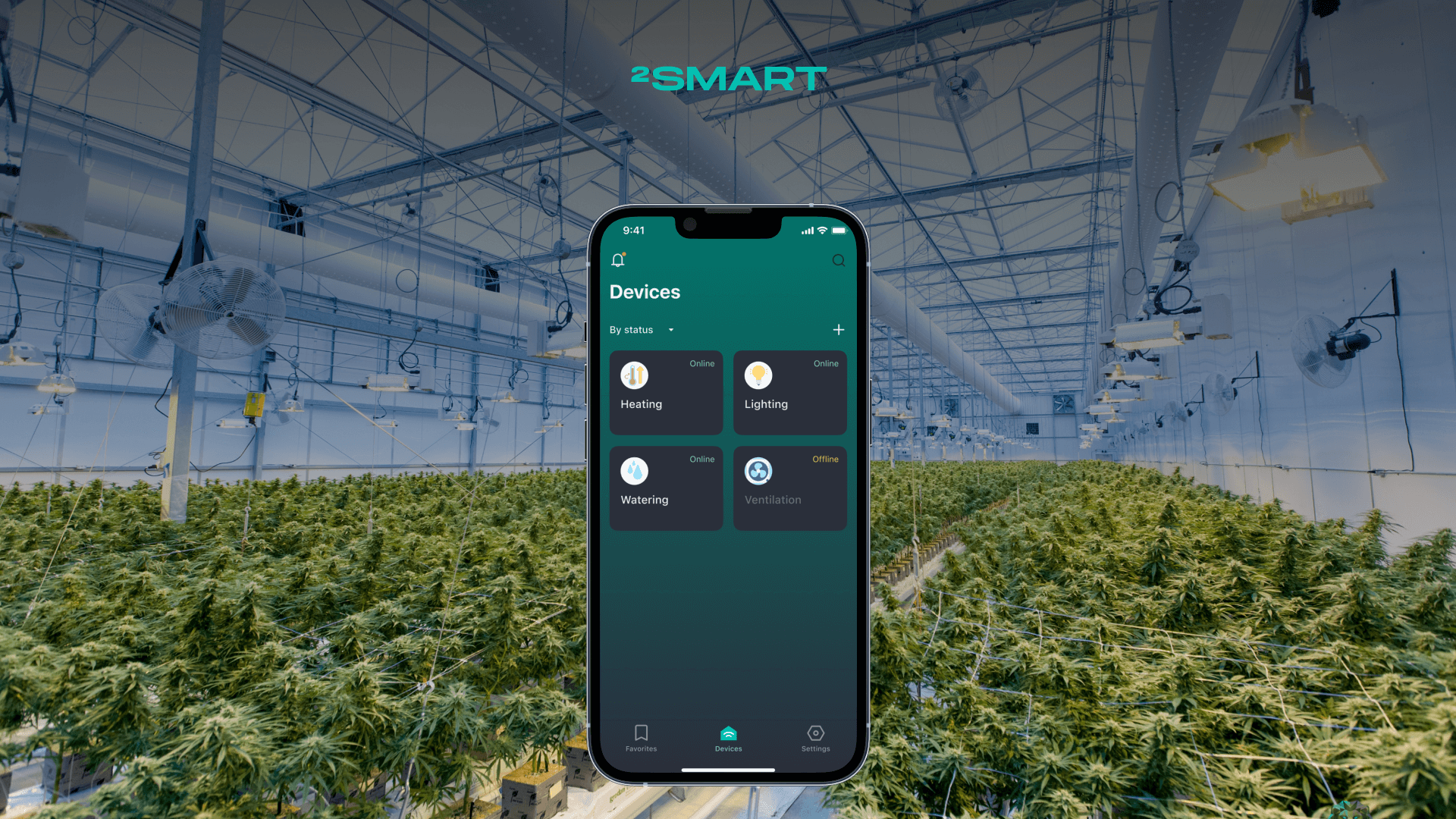
The end user can only manage the devices that are available to them and edit their account. The end user has access to a mobile application where they can start the pairing procedure to link the device. The application gives the end user the device management capabilities the product vendor configures. The end user can also log into the business platform web application, where they will only have access to the “My Devices” section with a list of available devices and the ability to manage them through a browser.
Obviously, system administrators may be required to take on additional roles ranging from Company Admin to End User. For example, help desk workers might need permissions to manage devices but not access to manage users, companies, and roles. There can be dozens of such cases, so the IoT Business Platform allows the creation of custom roles.
Custom Roles
Since any role in the system is described as a set of permissions to perform specific actions, the concept of permissions is considered whenever possible in developing any new functionality of the Business Platform. When extending an existing functionality, it is embedded in the current permissions. When adding new functionality, further permission appears in the platform.
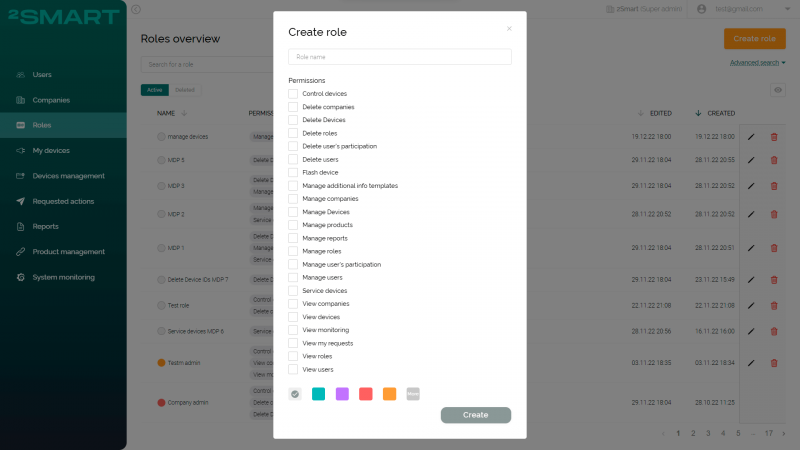
When creating a custom role, the administrator must specify its name and select the permissions that users with this role will receive. Currently, the list of possible permissions consists of more than 20 items. However, globally, we are talking about three types of actions with system entities, which include users, companies, roles, and devices: viewing, managing, and deleting.
Thus, the number of unique custom roles in the system is limited only by the number of possible combinations of permissions. Therefore, any enterprise can flexibly create any roles necessary to implement its business model.
For example, enterprise administrators can add one or more roles for developers, who are only involved in creating new products, writing firmware, and further maintenance. Custom roles can be made for a service department whose employees are only engaged in device maintenance but are not involved in device development or user management. Or vice versa, the list of permissions for a custom role can only relate to managing users, roles, and companies, if this is a role for employees of personnel services, business development department, etc.
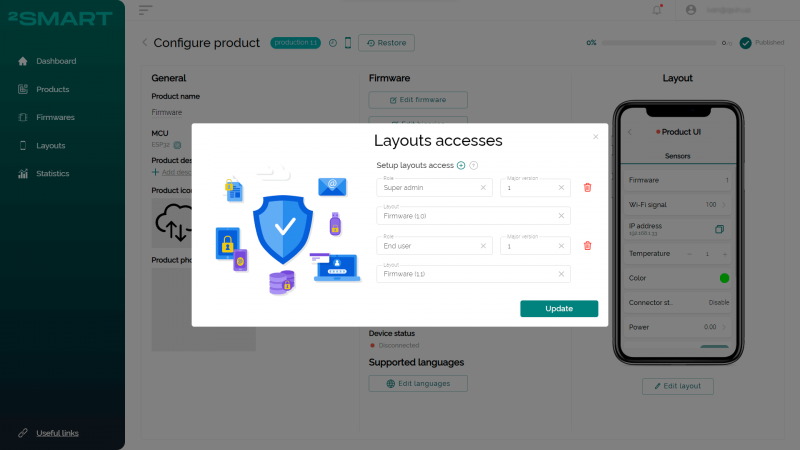
At the interface level of user interaction with connected devices, the platform also provides flexible customization options. When customizing the interface of a mobile application for managing a product using a no-code builder, developers can create different layouts for users with different roles.
This feature is intended to ensure that end users can only control the device while technical specialists have access to its telemetry and specialized sensors. However, as part of its business model, a company may also use this as an opportunity, for example, to offer its customers different levels of access to a device within separate tariffs. Access to the advanced functionality of the IoT product can be issued as an independent marketing offer.
As part of custom roles, administrators can also grant access to the IoT monitoring system, which is deployed out of the box for each Business Platform instance. Depending on the enterprise’s business model and the contract terms, both the 2Smart team and the customer’s internal staff or someone else can be responsible for system monitoring.
Thus, the flexible role customization functionality allows any enterprise that manages its IoT infrastructure using the 2Smart Business Platform to build processes in any way necessary. Administrators can use any logic without restrictions when adding new roles to the system.
If you want to know more details about the 2Smart Business Platform and user and role management functionality, you can order a demo of the platform by emailing contact@2smart.com
Don't forget to share this post!
Read Next
Let’s dive into your case
Share with us your business idea and expectations about the software or additional services.